What is Email Phishing?
Phishing is when a third party, usually a hacker or malicious website, uses the branding of a well known company to lure a user into exposing private information.
There are two types of email phishing schemes:
- Phishing emails that come to you
- Phishing emails that come from you
Phishing emails impersonate legitimate businesses to implant malware in an attachment or download or obtain login credentials. Phishing is the primary method of obtaining user information or passwords for attacks. You need to know how to protect yourself, your employees, and your business from phishing.
Identifying Phishing Emails
Phishing groups and hackers are constantly changing their patterns to improve both their targeting and the effectiveness of their emails in order to exploit users, but there are a few characteristics in common for every phishing email.
Phishing emails impersonate a strong brand
Big brands such as Paypal, UPS, Fedex, financial institutions, credit cards, banking and insurance industries are often impersonated to trick users into thinking an email message is authentic. Always ask yourself these three questions: Do you really have an account with that company? Is this the email address i provided for that account? Have you done anything with the account lately?
“From” domain and Return Path Domain will not match
It is relatively easy to spoof a “From” address. Email Standards allow ANY 3rd party to send email messages on the internet on behalf of another domain, otherwise hosting providers like Google and Outlook.com or bulk email providers could not send email for the business or personal domains they host. If for example, you recieve a message that looks like it came from PayPal, make sure the from address ends in PAYPAL.COM. There also may be text after the .com, for instance, PayPal.com.something.somethingelse. In this instance, you have a phishing email! –
There is an (often unexpected) attachment
If you are required to download anything that you did not ask the company for, then it is probably a phishing email and will most likely contain malware or viruses. PDFs or Word DOCs can contain malware payloads. They are trying to trick you into thinking that their fake attachment is real so that they can get personal, private or financial data from you. Don’t download attachments you did not ask for.
There is a sense of urgency
These kinds of emails will usually ask you to “take action soon” or it will cost you money. This sense of urgency makes you react before you think. Take a breath before acting on any email that looks really important.
Links on the page go to a different domain
Often a phishing email will include a link to a 3rd or 4th domain or just to an IP address. The goal here is to get you to click unsuspectingly on any link so they can further the con and grab your information when you attempt to login to their fake website. Sometimes the domains even look like subdomains or related domains. Always check links before clicking on them.
It is always best practice to open a clean window and navigate to the company’s website and login to your account from there to check on the issue. for Example, if you received an urgent email from Your Bank, either open a new browser window and go directly to your bank’s website by typing in the address yourself, or give your bank a call.
Quality Varies
Some phishing emails, look good on the surface. For example, the logos look correct, the fonts and color scheme are appropriate and some of the language is even straight from legitimate emails. However, when you read deeper you can see spelling mistakes, grammatical errors or other areas where it is clear the writer was not a native English speaker.
Our Spam Filter Has You Covered
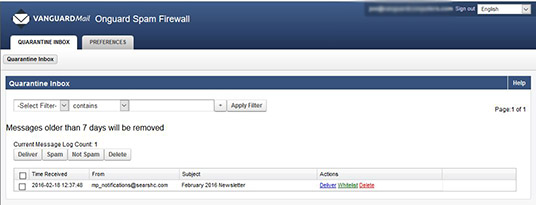
While no spam filtering solution exists that can eliminate this problem, our spam filtering has intelligent, adaptive, and learning based heuristics capabilities, allowing it to detect and block most of these emails before they ever hit your inbox. While having spam protection helps, its always up to the end users to follow these guidelines and become aware of these warning signs.
[su_button url=”http://www.bulldogtechinc.com/services/exchange-email-archiving/” target=”blank” background=”#bf1e2e” color=”#ffffff” size=”10″ wide=”no” center=”yes” icon=”icon: arrow-down” icon_color=”#ffffff”]Learn More About Spam Filtering & Email Hosting[/su_button]