
Read Article at CNN Business
New York (CNN Business)In one of the biggest data breaches ever, a hacker gained access to more than 100 million Capital One customers\’ accounts and credit card applications earlier this year.
How Can We Help You Today?

Read Article at CNN Business
New York (CNN Business)In one of the biggest data breaches ever, a hacker gained access to more than 100 million Capital One customers\’ accounts and credit card applications earlier this year.

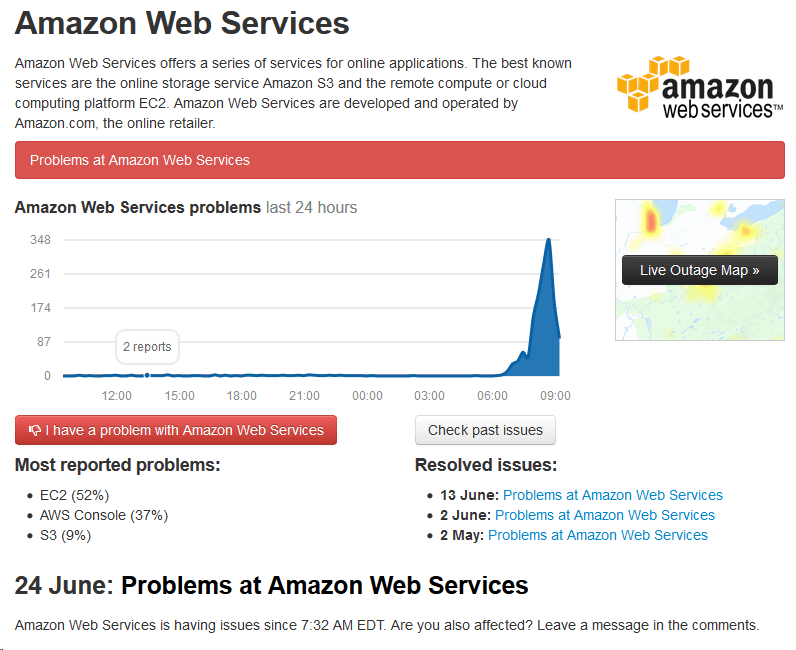
Bulldog Alert: Amazon Web Services was having connectivity issues today beginning at 7:32 AM EDT, confirmed by down detector. Issues have since been resolved and are blamed on an external internet provider. Even Amazon can have internet issues!
Let us know if you experience any connectivity issues with any of our hosted services. At this time all of our systems are running normally.

Quest Diagnostics, as well as Lab Corp, two of the largest testing providers in the country, announced nearly 12+ million customers may have had personal, financial and medical information leaked due to an issue with one of its vendors.
Quest said it was notified that between Aug. 1, 2018, and March 30, 2019, that someone had unauthorized access to the systems of AMCA, a billing collections vendor.
“(The) information on AMCA’s affected system included financial information (e.g., credit card numbers and bank account information), medical information and other personal information (e.g., Social Security Numbers),” Quest said in the filing.
While customers’ broad medical information might have been compromised, Quest said AMCA did not have access to actual lab test results, and so therefore that data was not impacted. Read More at NBC
One day after Quest Diagnostics reported that nearly 12 million of its patients were potentially affected by a malicious breach of third-party bill collection vendor American Medical Collection Agency (AMCA), fellow clinical testing firm LabCorp acknowledged that roughly 7.7 million of its customers may be affected by the same incident.
Burlington, North Carolina-based LabCorp publicly disclosed the disturbing news yesterday in a Securities and Exchange Commission 8-K filing, warning that patient data it supplied to AMCA was exposed in the incident, which took place from Aug. 1, 2018 through March 30, 2019. Such information may include names, birth dates, addresses, phone numbers, dates of service, providers and unpaid balances.
Making matters worse, roughly 200,000 customers who paid LabCorp bills using AMCA’s web portal had their payment card information compromised, the LabCorp continued. According to the SEC filing, AMCA did not share the identities of these particular victims, but assured the diagnostics company that it had already begun to notify these individuals, and would offer them two years of identity protection and credit monitoring services.


November 2018. A Brooklyn business opens for their usual days work. Employees go about their morning activities preparing for the work day. Upon starting their computers, they begin to log into their emails and fire up their software applications. One employee after the other gets similar error messages “file can’t be found” when they try to access their data. They notify management who also receives the same errors.
Bulldog Tech receives the tech call. After we remotely log into the systems, we find their entire servers data drives have been formatted! All their data has been erased! After further investigation, we found that special software was loaded onto the server that not only removes the data but security wipes the system making it nearly impossible to recover using recovery software.
Further investigation of their router logs (all server logs were erased) shows at 2:31am the previous night, an IP logged into the server using remote desktop ports. Reviewing the server we indeed found remote desktop enabled – a security risk in itself. Reviewing the finding with the owner, he realized that he released a long time employee recently – not on the best of terms. Is it possible this employee logged into their system and erased the data? Why was not all passwords and remote access turned off after termination? Good questions owner could not answer nor though of.
What again could have been a major disaster was quickly rectified by OnGuard Remote Backup! OnGuard Remote Backup was able to restore all customer data quickly and put them back in business!
We discussed with owner to use our additional services of OnGuard Defender, and security auditing as well as put in place an employee manual that addresses items upon termination. Basically a security checklist! Its your business, only you can protect it!

We received a call this week from a long time customer, a plumbing company that relies on SAP software to conduct their business; stating they could not access their server drive. Theyre business was stopped in it’s tracks.
Encryptionware garbled (encrypted) all the data including their SQL databases. We instructed them to immediately power down the system while we logged in to each workstation and ran a full virus scan. We found one of the receptionists initially was infected via an email attachment (via AOL), which executed code that scanned for accessible drives and encrypted any data found.
This customers business was stopped! Their service techs did not have access to their stops, accounting data was lost and the local attached backup drive was found to also be encrypted.
What could have been a major disaster, was mitigated by Bulldogs OnGuard Remote Backup. After our technicians reloaded the main server, ONGuard was able to recover all data files & SQL databases within 20 hours from the previous nights backup.
After less than a day, our customer was back in business thanks to OnGuard backup.
As a result, we discussed with the customer to migrate away from AOL email and move to our secure exchange servers as well as use our OnGuard Defender package to help mitigate future attacks.
This was a Win-Win for all!
If your data secure? Learn more about our OnGuard Remote Backup and protect your company today!